Security Focus Report FAQ
Security Focus Report FAQ
What is a Security Focus Report?
A Security Focus Report is a summary of security data for one department or school. It brings together data from three security tools: Amp, Qualys, and Spirion. A report consists of two documents: a one-page Security Brief and a searchable Excel sheet with several tabs. The first summarizes vulnerability data for the entire department. The next tab list all Severity 4 and 5 vulnerabilities in a searchable format. There may be individual tabs for computers that have the most data likely to be restricted or sensitive. There may also be a chart listing additional computers with 100 Spirion matches or more, which DoIT considers the threshold for an action item.
When are Security Focus Reports generated?
Reports go out once a month, in the third week of the month. (Microsoft's Patch Tuesday is in the second week. Data is aggregated for the reports a week later, after automatic patching cycles have finished.)
Can I request a different reporting schedule?
Currently no. The process of aggregating data from different tools is labor intensive, and is done only once a month. Departments that receive monthly reports get them nine or ten days after Patch Tuesday. When a department requests a report for the first time, they recieve a scheduled report the next time they are generated.
What does the Security Brief include?
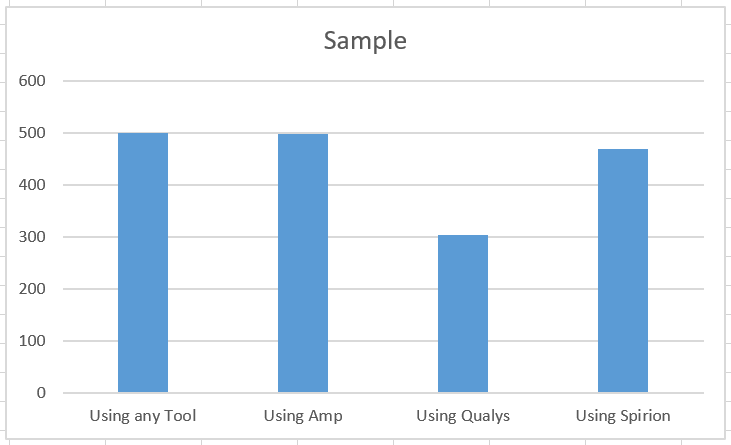
- A paragraph documenting the number of endpoints the department has visible in DoIT security tools, how many use Amp, how many use Qualys, and how many use Spirion.
- A bar graph illustrating those same statistics.
- Recommended actions to address the most serious security risks, if applicable.
What does the Excel Report include?
This depends on the department, especially the extent to which Spirion is used, and the number of endpoints where Spirion detects sensitive data.
The first tab is the Vulnerability Summary, and can have up to four tables, depending on the data:
- Most Widely Used Vulnerable Applications. It lists applications that need patching on the most computers, regardless of the number of specific vulnerabilities in each application. In many cases, deploying a patch can address a dozen or more vulnerabilities per computer, and in a large department that may apply to hundreds of computers.
- Obsolete Operating Systems. Windows 7 is the most common, but Windows XP and old versions of iOS and Linux can be reported. These computers should be upgraded or retired if at all possible, as outdated operating systems are not supported, and have numerous vulnerabilities for which there is no patch. This table is omitted if Qualys has not detected any obsolete operating systems in the department.
- Other End of Life Software. As with operating systems, obsolete software is not supported and usually has multiple vulnerabilities with no patch available. This software should be upgraded or uninstalled if at all possible. As with the Obsolete OS table, this one may be omitted if no obsolete software has been detected.
- Most vulnerable hosts. A common question is how a single computer can have over 200 specific vulnerabilities. In most cases it is because a major application has not been updated/patched in over a year, allowing vulnerabilities to accumulate. This means that patching one or two applications often makes a machines far more secure.
The second tab in the Excel document lists all Severity 5 and Severity 4 vulnerabilities that Qualys detected for the entire department. In larger departments this list can include over 50,000 specific vulnerabilities. While this is not as convenient as the summary tables, it can be searched and filtered in numerous ways: by vulnerability, application, computer, vulnerability age, and more.
If a computer has over 1000 Spirion matches, this is a high-risk machine. Of those, five with the most Spirion matches have separate tabs on the Excel document, which includes severity 4 and 5 vulnerabilities if applicable, the number and location of Spirion matches, and any serious security events detected by Amp. These tabs are omitted if Spirion does not detect 1000 matches on any one computer.
The last tab on the Excel document lists any additional computers with over 100 Spirion matches in tabular form, listing only the number of Spirion matches, the number of vulnerabilities, and the number of security events if applicable. Cybersecurity considers 100 matches the action threshold. If no computer has 100 or more Spirion matches, this tab is omitted.
Why doesn't my department get a report?
This is an "opt-in" service. Reports are sent to departments that request them.
How do I requests a report?
Submit requests to Qualtrics EForm
When submitting a request, please provide as much information as you can about UDDS codes and Spirion tags your department uses. If you aren't sure, leave blank. Cybersecurity will contact you if more information is needed.
What tags and/or codes should I include when I make a request?
What range of computers to include in the scope of the report depends on who has responsibility for securing them. Some schools centralize IT security and use a single report for the entire school, including thousands of computers. Other schools delegate security work to an IT staff member in a specific department, who receives a smaller report limited to his or her area of responsibility.
When I receive a report, what are the next steps?
The Office of Cybersecurity provides the reports to help departments secure their IT assets. They use the data in various ways, depending on need. There is a KB that details one possible workflow for reducing IT security risks using report data, but it should be considered an example, not a rule. See KB#113400.
What if there is a problem with my report?
There is a troubleshooting section in KB#113400.